Overview
This document helps you, deploy OVA on the VirtualBox, and set up Seqrite Endpoint Security server.
OVA (Open Virtualization Appliance) file contains a compressed version of a virtual machine. When you deploy an OVA file, the virtual machine is extracted and imported into the virtualization software installed on your computer.
The OVA build file is provided to address any of the following scenarios at the customer end.
- CentOS machine is not available.
- Only Windows machine is available.
- The customer does not want to dedicate a CentOS machine for installing Seqrite Endpoint Security.
This OVA will create a CentOS machine on top of the VirtualBox and then you can proceed through the configuration of the pre-installed EPS server.
OVA Details
- OVA File name: EPS8.1_CentOS7.9.ova
- Oracle Virtual box version: 6.1.38
- RAM: 8 GB
Prerequisites
- Windows Environment – Windows 10 and above; Windows server 2019 and above.
- Virtual Box version 6.1.38
- Disk space: 60 GBs and above
- RAM: 16 GBs or above
- Processor: 4 Core (x86-64) or above
- The VT-x must be enabled in the physical machine’s BIOS.
- EPS8.1_CentOS7.9.ova build file
-
Keep the following details ready and handy.
- Product Key
- Static IP Address
- Gateway
- Subnetmask
- DNS
Step 1: Deploy OVA on VirtualBox
- Download and install Oracle VM VirtualBox on Windows machine.
- Open the VirtualBox.
- Go to File > Import Appliance.
- In this step, choose a virtual appliance file to import. Click Browse and select EPS8.1_OVA file.
- Click Next and follow the wizard.
-
Click Import.
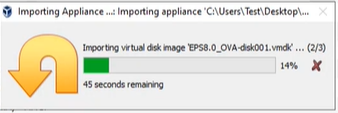
When the Import is complete, VirtualBox creates VM with CentOS. On this, you will configure the pre-installed EPS 8.1 server.
Start the VM.
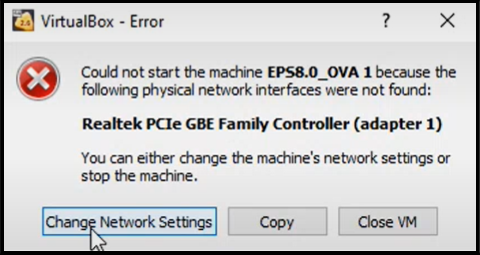
The Network Error prompt appears.
-
Click Change Network Settings. The network settings window appears.
The network adapter details of the system appear.
-
Click OK.
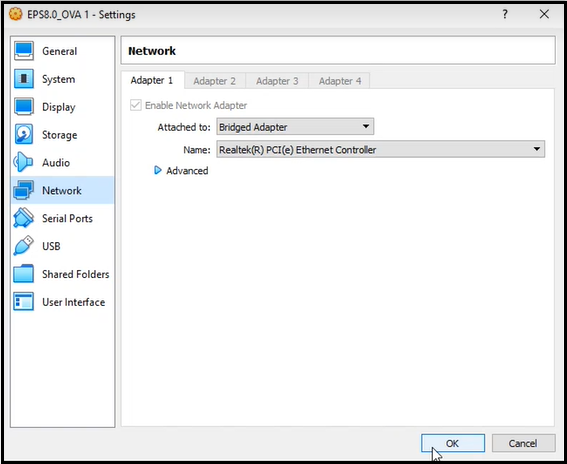
OVA is deployed successfully on the VM.
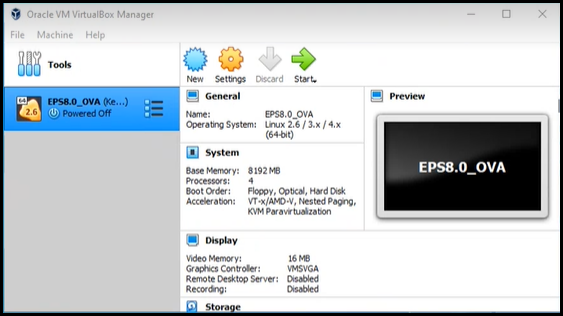
-
Click Start icon to start the VM.
The VM is ready for use.
Step 2: Configure EPS Server
- On the VM, login with the given credentials.
Note: It is recommended to change the password after installing the EPS server.
-
Provide the following details one after another and hit [Enter].
- Static IP Address
- Gateway
- Subnetmask
- DNS
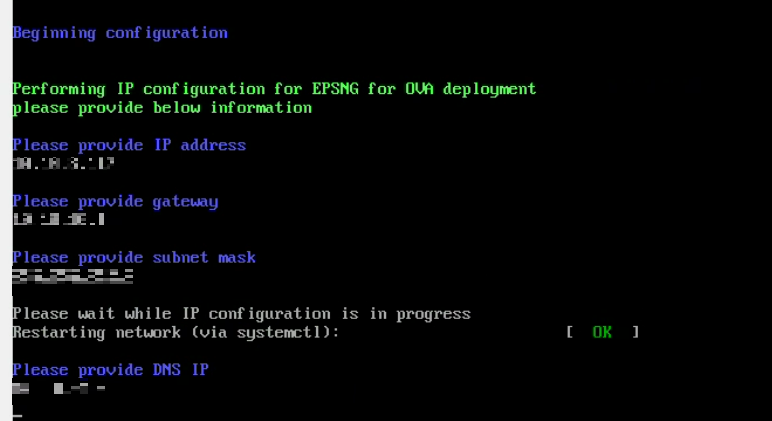
-
After internet connection is successful, enter Host name. Hit [Enter].
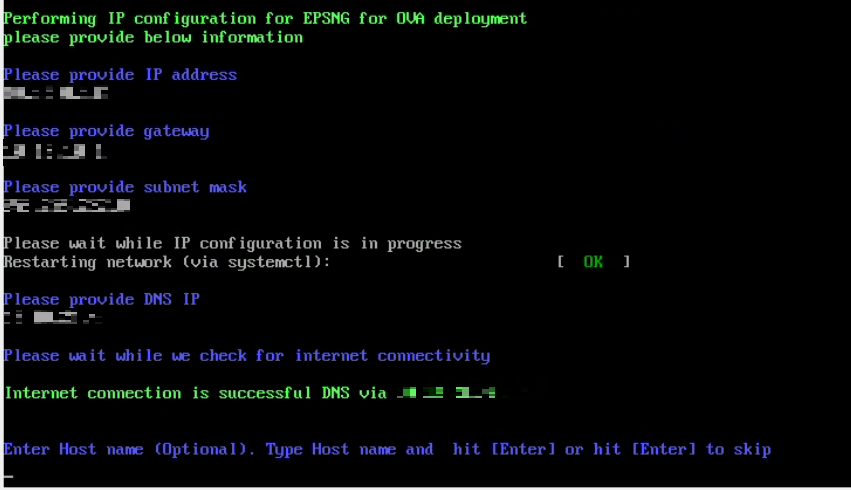
- Software License agreement appears. Read the License Agreement carefully. Installation and usage of Seqrite Endpoint Security is subject to your formal acceptance of the Seqrite Endpoint Security end-user license terms and conditions. To continue, hit [Enter] or press R key to read more.
-
Terms & Conditions appear. To continue, hit [Enter] or press R key to read more. To continue, type A and hit [Enter] to accept the terms and conditions; D option is to decline. If you decline, the installation process is stopped.
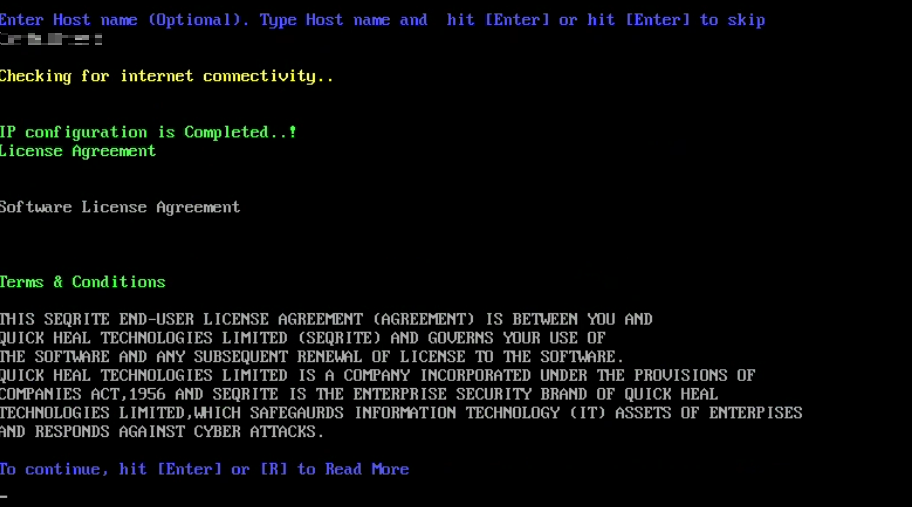
- Please wait till configuring the system for user, which may take 5 to 6 minutes.
-
The Proxy Settings screen appears. If you are using a proxy server to connect to the Internet, type 1 and hit enter.
If you want to continue without enabling Proxy Settings, type 2 and hit enter. The Proxy Setting information is used by EPS server for internet connectivity, activation and for downloading updates.
To enable and configure proxy settings:
a. Type the IP address of the proxy server or domain name (For example, proxy.yourcompany.com) and hit [Enter].
b. Type the port number of the proxy server (For example: 80) and hit [Enter].
c. Type 1 to Authenticate to connect through the Proxy server. Type 2 to continue without authentication.
d. Type User Name.
e. The success message appears if the connection to the proxy server is successful.
-
The Product Key screen appears. Enter the Product key in capital letters without the hyphen. The Product Key will be validated. The success message appears.
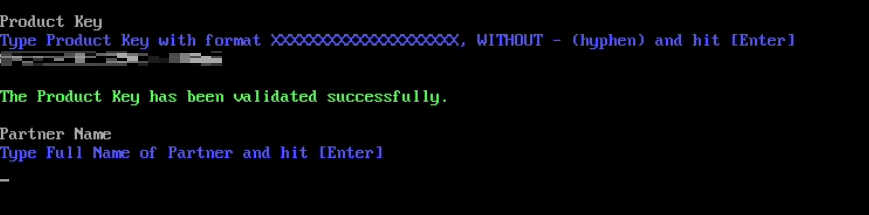
-
The Customer Information screen appears. Type information about the customer step by step. This information is important to activate Seqrite EPS on your machine.
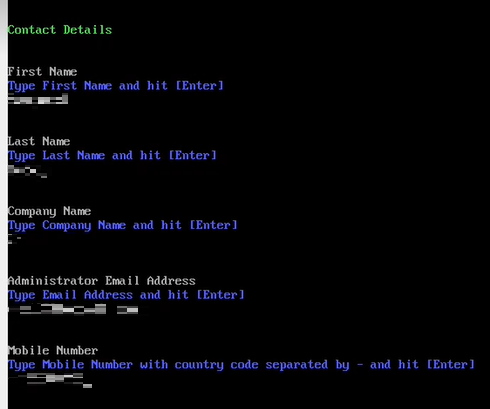
Note: The maximum length for the First name is 50 characters.
-
The Authentication screen appears. Create Seqrite Endpoint Security administrator password to access the Web console and endpoint password to access the endpoint settings at the endpoint side.
a. Type in Administrator Email Address and hit [Enter] or you can continue with the Email address appeared. To continue, hit [Enter].
b. Type in your password and hit [Enter]. Type password again to confirm the password and hit [Enter]. You cannot view the typed password.
c. You can provide client credentials. This is optional. Type 1 to specify client credentials and hit [Enter]. Type in client password and hit [Enter]. Type client password again to confirm the password and hit [Enter]. You cannot view the typed password.
d. This helps prevent unauthorized users from accessing the Web console and make changes in your settings or remove the endpoints.
e. Type 2 to continue without providing client credentials and hit [Enter].
-
The installation summary screen appears. Activation and Server Configuration data is displayed. Please note the EPS console URL.
a. Type 1 to save summary file and hit [Enter].
b. Type 2 to continue without saving and hit [Enter].
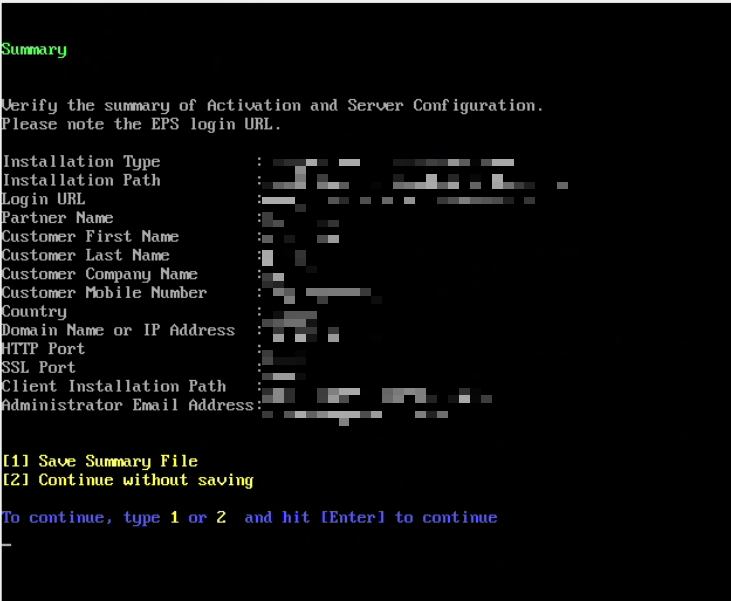
-
The installation process starts. Tenant onboarding starts. Success screen appears.
a. Type Y to continue using the system and hit [Enter].
b. Type N to log out and hit [Enter].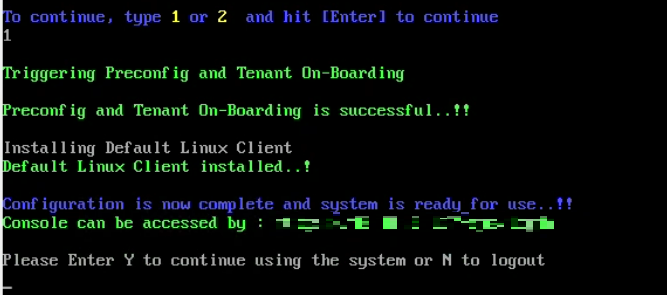
-
If you enter Y, the following screen appears.
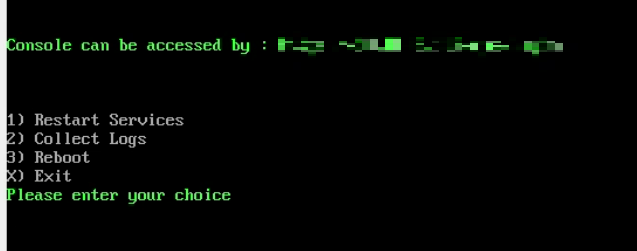
Enter your choice and hit [Enter].
Step 3: Log on to EPS Server
-
Paste the console access URL in any bowser. Example: https://
/login/eps Supported Web Browsers:
- Google Chrome 62, 63, 64 or 65
- Mozilla Firefox 56, 57, 58, 59, 62, 64 or 65
- Microsoft Edge.
- Provide the credentials.
Seqrite Endpoint Security console is ready to use.
Exiting the set up
You can exit from the set up process by pressing Control C keys.
Confirmation message will appear. Again, press Control C keys to exit the setup.

